TELP secures provisioning process from programmer to target
Segger has released the Target Encrypted Link Package (TELP) to ensure the protection of intellectual property (IP) from end to end, including the last few inches to the device.
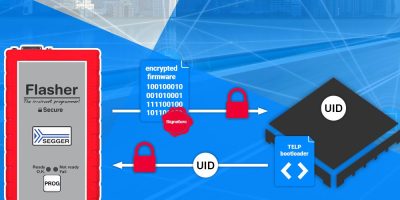
Flasher Secure, Segger’s flash programmer for authenticated off-site production, protects the firmware image at all stages of the provisioning process between IP owner and contract manufacturer. TELP secures the link from programmer to target and ensures that captured signal traces cannot be used to clone devices by simply replaying the programming sequence. Every device is programmed using mutually-agreed, unique session keys for the encrypted link. Without those keys the captured trace is useless, explained Segger. Together, they ensure end-to-end IP security and protection against attacks of any kind.
The contract manufacturer never has access to the clear text of a firmware image and both the manufacturer and IP owner can protect IP from being copied, cloned or produced without authorisation. The Flasher Secure / TELP offers complete transparency for IP owners to seamlessly track the programming yield, device-specific data and programmer details. This unparalleled transparency is particularly crucial when outsourcing production to third-party locations, advised Segger. It added that the level of confidentiality is unmatched in the market.
“Flasher Secure and TELP are redefining the standards of secure programming,” says Ivo Geilenbruegge, Segger’s managing director. “Together they allow innovators to confidently bring their ideas to market, secure in the knowledge that their IP is protected all the way to the silicon.”
According to Segger, this is the only solution available today that provides end-to-end security for the entire workflow, from firmware sign-off to final production, while also providing interfaces for quality assurance and warehouse management.
TELP can be used to secure a wide range of microcontrollers, particularly protecting MCUs that do not come with built-in security features. There is no need for special processors or pre-programming required and no physical shipment.
Security is achieved using a combination of established and standardised cryptographic algorithms, cryptographically secure random number generators, and reliable key exchange algorithms.